The Drift Stack™ — Architecture v2.0
This page explains what Drift is, why it’s real, where it shows up, and why governance cannot be post-hoc. Drift Stack™ is an architecture — a governed specification — that formalizes invariants, admissibility, and correction as explicit layers.
If you only remember one line: LLM outputs are not “the system.” The system is execution authority — what can write state, trigger action, move money, revoke access, or commit irreversible outcomes.
Recommended Architecture Path
Drift Architecture
This page shows how the architecture operationalizes admissibility, enforcement, and externalized control in a real system.
This sequence is cumulative. Each layer builds on the one before it.
What Drift Is (and why it matters)
Drift is not “model hallucination.” Drift is a structural phenomenon: systems deviate from their intended invariants over time — across AI, organizations, institutions, economies, and human cognition — because authority paths are not constrained by enforceable boundaries.
- Drift is real: it appears across domains, not just in AI.
- Drift has an order of collapse: certain invariant failures predictably come first, and the rest follow.
- Governance cannot come post-hoc: once execution authority is permitted to act, “oversight after the fact” becomes narrative management, not control.
- Architecture establishes invariants: the system must be designed so invalid trajectories cannot form.
Drift Stack™ Operational Coherence Model
Drift Stack™ is organized around five layers: Identity, Frame, Coherence Boundary, Drift, and Correction. State reconstruction lives inside Frame. Admissibility, execution governance, pre-execution confirmation, and execution boundary enforcement live inside the Coherence Boundary.
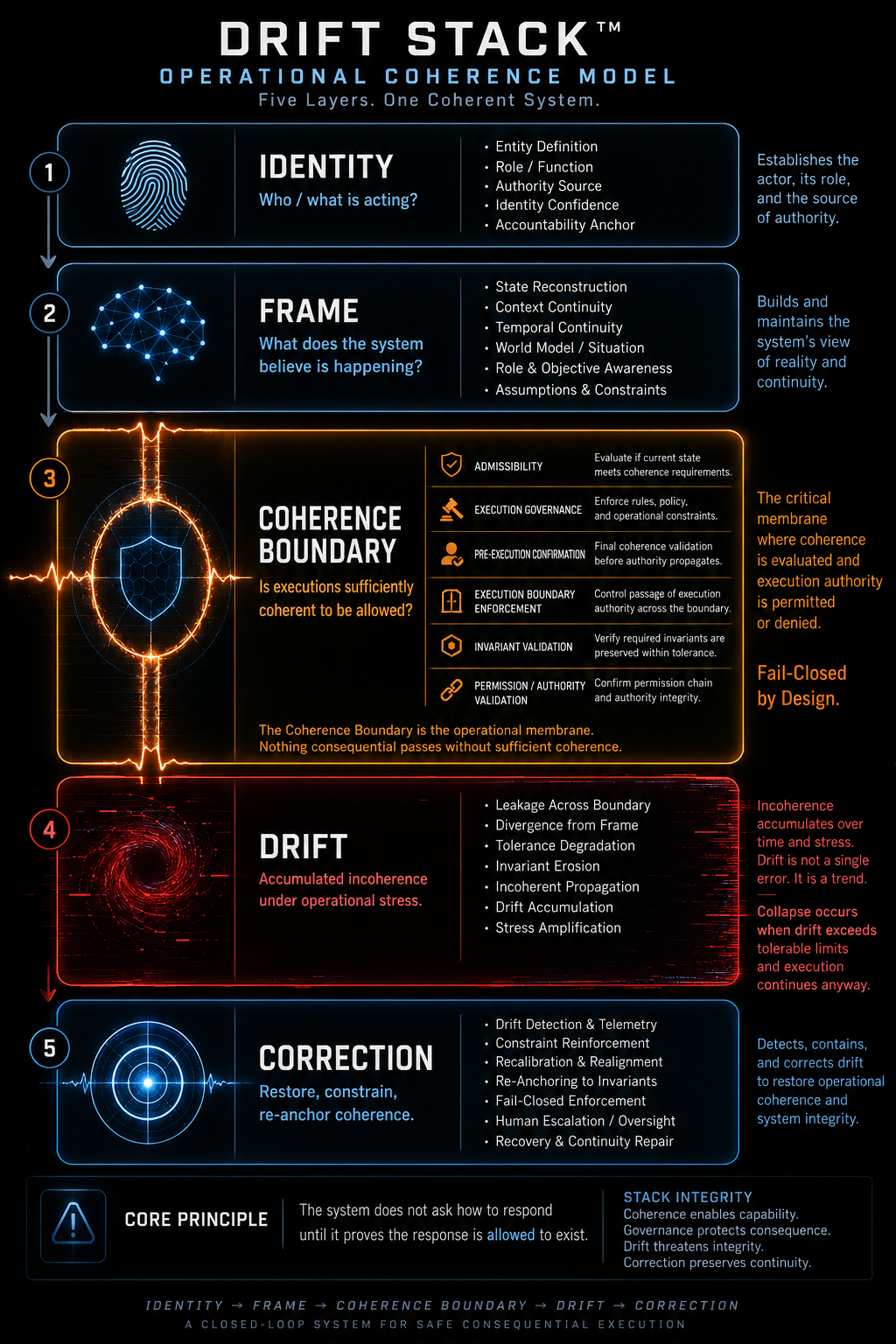
This model shows the containment structure of Drift Stack™: state reconstruction belongs inside Frame, admissibility and execution governance belong inside the Coherence Boundary, and drift accumulates when operational incoherence exceeds tolerable limits under consequential execution.
Drift Shows Up Everywhere
Drift Stack™ is supported by public writing, examples, and profession-specific entry points. The point is not that “AI is uniquely dangerous.” The point is that drift is a general failure mode — and AI simply makes it faster and harder to see.
LLM ≠ System
An LLM can generate text. A system can execute. The risk is not “bad text.” The risk is delegated execution authority: systems that can cause irreversible state changes based on unstable reasoning.
Drift Stack™ focuses on the authority path — what can act, what can write, what can trigger outcomes — and enforces structural invariants before execution occurs.
Architecture establishes invariants
Drift prevention is not a vibe. It is not “monitoring.” It is not “retries.” It is not “AI safety slogans.” It is explicit invariant structure — named layers that determine what can and cannot occur.
- Layers are named. Each layer has a purpose and constraints.
- Admissibility gates are explicit. They belong to a layer and enforce coherence boundaries.
- Governance must be pre-execution. If the gate is not enforced before action, you don’t have governance.
Admissibility gating ≠ external correction
These are complementary — not substitutes.
- Admissibility gating prevents the wrong action from happening in the first place.
- External correction prevents the right action from becoming wrong over time.
- Drift Stack™ shows how both must be architected as explicit layers, with defined boundaries and authority paths.
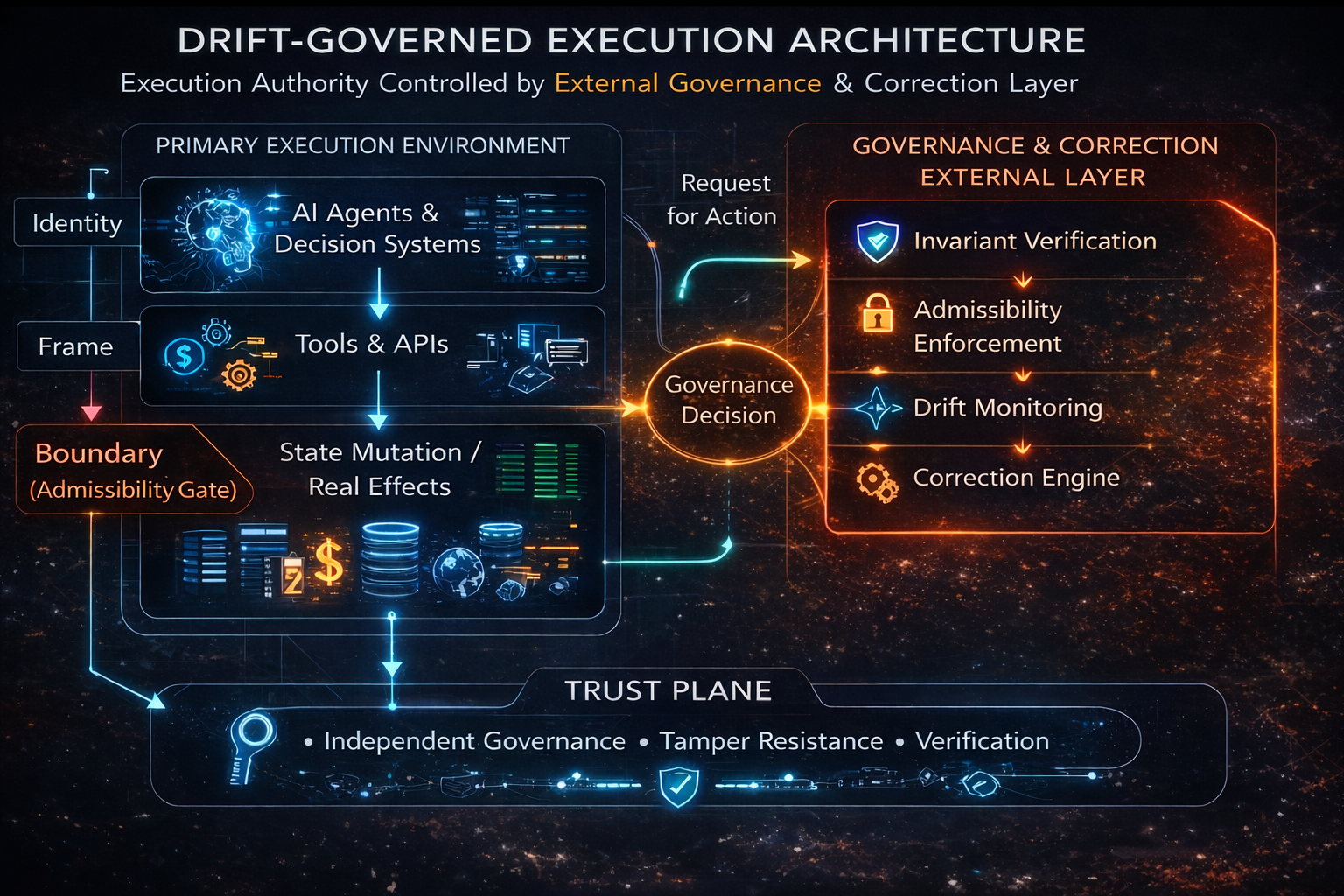
This public-facing view shows the authority path cleanly: execution requests action, governance resolves whether the transition is admissible, and correction remains external to the execution environment.
Rogue AI Protection (Mythos-Class Scenario)
A high-capability model does not create risk by itself. Risk emerges when capability is allowed to execute without constraint.
Whether the scenario is real, emerging, or hypothetical is not the point. The architectural question is:
What is your system allowed to execute?
Drift Stack™ does not rely on model behavior, detection, or post-hoc correction. It enforces admissibility before execution, ensuring that even highly capable or adversarial systems cannot produce irreversible outcomes without passing invariant constraints.
A system is not conformant because it sounds aligned. It is conformant only if Drift Stack™ structure and SAQ™ enforcement are both present before execution occurs.
THE ONLY QUESTION THAT MATTERS
DOES YOURS CONFORM?
If your system can take action, write state, trigger workflows, or influence irreversible outcomes, the real question is not whether it sounds safe. It is whether its architecture conforms before execution authority is trusted.
Conformance Evaluation →